Vegadream Casino ᐉ Bonus 2023 Erfahrungen und Test
Walk of Dreams
Content
- Vegadream Willkommensbonus-Paket – Bis zu 1650 € + 300 Freispiele ✔ Aktiv
- Häufig gestellte Fragen Vegadream Casino
- Unique Casino – 10 Euro kostenlos boni (keine Einzahlung erforderlich)
- Bonusspiele
- Cobra Casino
- Bis Zu €500 Match Bonus (Exclusive VIP Silver Club) de Vegadream Casino
- Casino-Tischspiele
- FAQs zu unseren Vegadream Casino Erfahrungen
- Geschichte des Vegadream Online-Casinos
- Bis Zu €250 Match Bonus (Exclusive VIP Gold Club) de Vegadream Casino
- Woran erkennt man, dass das Vegadream Casino seriös ist?
- Bonusbedingungen für den Bonus ohne Einzahlung
- Slots
- Vegadream Live Casino
- Vegadream Bonus ohne Einzahlung – 20 Freispiele ✔ Aktiv
- Casino- Boni – auch für Stammkunden
- Vegadream Casino
- 🥇 Wie fällt die Vegadream Casino Bewertung der Spiele aus?
- Vegadream Casino Erfahrungen – Test und Bewertung 2023
- Anbieter der Casino-Spielsoftware
- Vegadream Casino App und Mobile Webseite
- Live Dealer Spiele
- Jackpot Spiele
- Mit welchen Zahlungsarten man im Vegadream Casino bezahlen kann
- Spielerschutz und Sicherheit im Vegadream Casino
- Vegadream Casino Einschränkungen
- Das Spielangebot in Zahlen
- Spiele bei Vegadream Casino
- Vegadream Bonus – alle Bonusaktionen in der Übersicht
Bei der Entwicklung der Spiele wurde in den meisten Fällen der Mobile First Ansatz bedacht. Das heißt, von der ersten Codezeile bis zum Release wurde die Darstellung der Games auf mobilen Endgeräten wie Smartphones und Tablets in den Vordergrund gerückt. Grundlage hierfür sind Entwicklungen auf Basis von HTML5 mit flexiblen Grid-Systemen, die Ihr Lieblingsspiel auf jedem mobilen Endgerät gut aussehen lassen. Damit können Sie nicht nur am Desktop PC, sondern auch auf dem heimischen Sofa und von unterwegs Ihre Lieblingsspiele spielen. Auf dem Desktop-PC lässt sich die Größe durch Verschieben des Browsers anpassen.
- Die Suche ist ebenfalls etwas gewöhnugsbedürftigt, funktioniert aber dennoch gut.
- Jedoch haben Sie bei allen Bonusangeboten 30 Tage ab dem Moment der Aktivierung Zeit, diesen an den zulässigen Spielen umzusetzen.
- Welcher Glücksspiel-Enthusiast würde nicht einmal gerne nach Las Vegas und den Strip entlang schlendern, um sich von Casino zu Casino zu spielen?
Dies ist ein absoluter Knaller-Bonus, denn Sie müssen Ihre Gewinne nicht einsetzen. Mit den 100 Freispielen gewinnen Sie Geld, und Sie können diese Gewinne abheben, wann immer Sie wollen. Wenn Sie jedoch 500 € einzahlen möchten, erhalten Sie vom Casino einen Bonus von 500 €. Sie entscheiden, wie viel Geld Sie spielen möchten und wie viel Geld Sie von Vegadream erhalten. Beachten Sie, dass Sie Ihr Bonusgeld 30 Mal umsetzen müssen, bevor Sie eine Auszahlung beantragen können.
Vegadream Willkommensbonus-Paket – Bis zu 1650 € + 300 Freispiele ✔ Aktiv
Es ist wirklich so, dass es keinen Abschnitt mit den Tischspielen gibt. Solche Spiele, wie Roulette, Blackjack, Baccarat, Poker und andere sind im Abschnitt Live Casino präsentiert, das heißt, nur das Spiel mit Live Dealer ist verfügbar. Wenn Sie gewöhnliche Spiele dieser Kategorie genießen wollen, beachten Sie Unislots Casino oder SlotWolf Casino. Dort gibt es die Abschnitte der gewöhnlichen Tischspiele, ohne Live Dealer und mit Demonstrationsmodus. Außer dieses nicht bemerkenswerten Nachteils ist Vegadream Casino eine ausgezeichnete Wahl für das Spiel für reales Geld. Das Online Casino bietet einen großzügigen Willkommens Bonus, Saisonaktionen und regelmäßige Turniere an https://vulkan-vegas.de.
- Ganz grob lässt sich unser Portfolio in die Kategorien Neue Spiele, Slots, Megaways, Games mit hoher Volatilität sowie Jackpotspiele und Live Casino einteilen.
- Vegadream belohnt Sie auch mit 100 Freispielen mit Wetteinsatz!
- Abgerundet wird das Angebot durch schnelle und sichere Zahlungsoptionen, einen zuverlässigen Kundensupport und eine benutzerfreundliche Website.
- Unsere ausführlichen FAQs bieten einen Überblick über die wichtigsten Fragen, die in der Vergangenheit gestellt und bereits beantwortet wurden.
- Beispielsweise wäre es schön, wenn die Tischspiele eine eigene Kategorie bekämen.
Sie können die Liste der Zahlungssysteme vom Vegadream Casino Online, Hauptvor- und Nachteile der Spielplattform sehen. Wir haben die maximale Zahl der ehrlichen und aktuellen Information gesammelt. Wollen Sie im Vegadream Casino spielen, aber Sie wissen nicht, womit Sie anfangen sollen? Um alle Fragen noch vor dem Spiel zu beantworten, empfehlen wir die Bekanntschaft von der Hauptinformation zu starten. Ich bin Rolf Brinker, der Experte von Playcasino.com für die deutschsprachigen Casinomärkte. Aufgrund meiner umfangreichen Berufserfahrung bin ich überzeugt, dass ich ein breites Wissen über Online Casinos, Casinospiele, Boni, die Glücksspielregulierungen und vieles mehr besitze.
Häufig gestellte Fragen Vegadream Casino
In unseren Vegadream Erfahrungen konnten wir zudem feststellen, dass eine Auszahlung über ein E-Wallet von Neteller und Skrill meist schon innerhalb weniger Stunden durchgeführt wird. Einzahlungen sind, wie in fast jedem Online-Casino, sehr einfach und schnell über die Bühne gebracht. Sie müssen sich einfach nur anmelden und schon können Sie über das Hauptmenü zu den Zahlungen gehen und Ihr Konto aufladen.
- Freispiele sind ebenso ein Bestandteil wie weitere lukrative Bonusangebote für Bestandskunden.
- Dazu gehört beispielsweise, dass der Einzahlungsbetrag bei 20 Euro oder mehr liegen muss und der Casino Bonus nicht übertragbar ist.
- Außerdem garantiert die Lizenz der Glücksspiele von Malta die Datenschutzpolitik von der Seite des Casinos.
Trotzdem ist es möglich, das Bonusgeld zu nutzen, um im Live-Casino zu spielen. Wir hoffen, dass in Zukunft auch spezielle Angebote für die Live-Casino-Fans verfügbar sein werden. Unseren Kunden bieten wir eine übersichtliche Benutzerplattform. Der Registrierungsprozess ist unkompliziert und Ihre Lieblingszahlungsmethoden sind schnell angebunden. Auch in Puncto Kompatibilität bieten wir unseren Kunden die Möglichkeit von vielen mobilen Endgeräten und Desktop-Betriebssystem unser Casino zu erreichen. Das einzige was Sie brauchen ist ein Internetzugang sowie einen gängigen Browser (z.B. Edge, Chrome, Firefox), mit dem Sie das Vegacasino aufrufen können 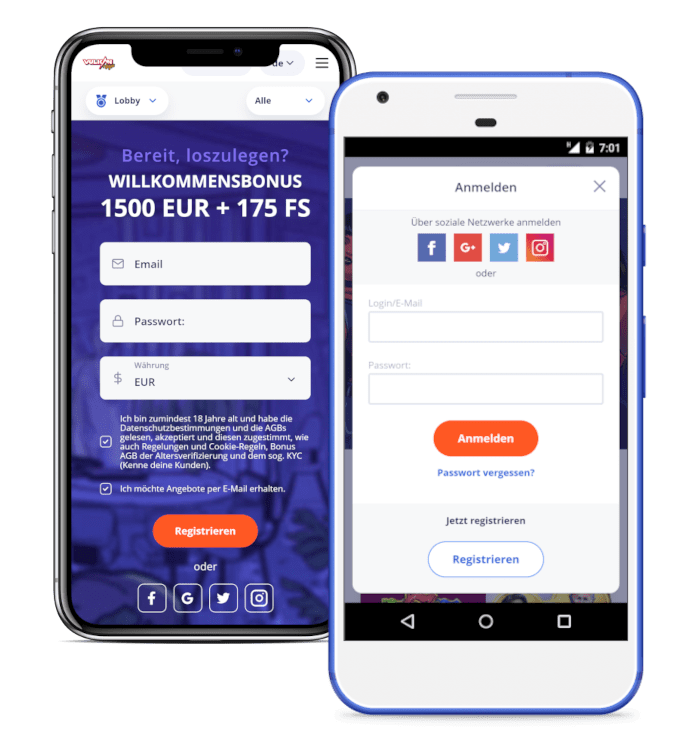 .
.
Unique Casino – 10 Euro kostenlos boni (keine Einzahlung erforderlich)
Ganz gleich, ob Sie auf der Suche nach bester Live Casino Unterhaltung sind oder mit kleinen oder größeren Spieleinsätzen die Video Slots zum Glühen bringen möchten. Das Vegadream Casino punktet mit einer hervorragenden Spielauswahl und fairen Auszahlungsquoten. Das Vegadream Casino bietet seinen Spielern die Möglichkeit, die Spiele auch auf einem mobilen Gerät zu genießen. Die Benutzerfreundlichkeit wurde verbessert, indem die Menüs und Tasten für ein besseres Spielerlebnis auf einem Touchscreen neu angeordnet wurden.
- Die Willkommensaktion mit einem hohen Startguthaben und vielen Freispielen kann sich sehen lassen.
- Wenn Sie sich bei der Suche lieber mehr Zeit lassen möchten, können Sie Ihr Wunschspiel auch nach Kategorie sortiert suchen und finden.
- Grundlage hierfür sind Entwicklungen auf Basis von HTML5 mit flexiblen Grid-Systemen, die Ihr Lieblingsspiel auf jedem mobilen Endgerät gut aussehen lassen.
- Es wird Ihnen nie langweilig und Sie können immer einen interessanten Bonus kassieren.
- Dort gibt es die Abschnitte der gewöhnlichen Tischspiele, ohne Live Dealer und mit Demonstrationsmodus.
- Die Support-Mitarbeiter des Kundendienstes stehen Ihnen jedoch auch über die E-Mail-Adresse [email protected] für Ihre Anliegen zur Verfügung.
Sollten Sie einmal technische Fragen haben, können Sie uns gerne per Mail oder über unser Kontaktformular erreichen. Neue Spiele finden Sie schnell und einfach über das Tab “Neue Spiele” auf unserer Hauptseite. Diese Kategorie ist durchgemischt und enthält Games aus all unseren Kategorien.
Bonusspiele
Hier sind eure Optionen in dieser Spielbank jedoch nicht ganz so vielfältig. Trotzdem findet ihr eine gute Auswahl an Roulette sowie Kartenspielen à la Blackjack oder Poker und noch einiges mehr. Alternativ ist meine Vegadream Erfahrung mit diesen Spielen im Live Casino auch sehr gut ausgefallen. Wenn Sie viel Geld gewinnen, können Sie auch viel Geld abheben. Sie müssen Ihren Einsatz nur innerhalb von 30 Tagen nach Erhalt des Bonus abschließen. Alle Besucher von BestBettingCasinos.com erhalten einen exklusiven Bonus ohne Einzahlung bei Vegadream Casino.
- Ganz gleich, ob Sie auf der Suche nach bester Live Casino Unterhaltung sind oder mit kleinen oder größeren Spieleinsätzen die Video Slots zum Glühen bringen möchten.
- Die Glücksspielseite bietet klassische und moderne Spielautomaten mit 3 bis 9 Walzen, einer unterschiedlichen Anzahl von Linien und Preisfunktionen.
- Die beliebtesten Spiele aus dieser Kategorie stammen aus den Software-Schmieden von Pragmatic und Mega Wheel.
Wenn Sie zu Ende gescrollt haben, können Sie über die zentrierte Schaltfläche “Weitere Spiele laden” mehr Games zur Ansicht laden. Diese Spieleauswahl ändert sich kontinuierlich, da wir dem Vegadreams Casino stetig neue Slot Games und spannende Live Spiele hinzufügen. Wir bieten eine große Auswahl an Spielen, einige Klassiker wie Book of Shadows, aber auch echte Raritäten, von denen selbst High Roller noch nie gehört haben.
Cobra Casino
Leider gibt es für keines dieser Spiele eine Demoversion, sodass man immer mit Echtgeld spielen muss, um es auszuprobieren. Direkt nach Ihrer Anmeldung bei Vegadream haben Sie die Möglichkeit, mit Ihrer ersten Einzahlung einen der drei Willkommensboni zu aktivieren. Am besten verwenden Sie hierfür einfach unseren Link, um sich direkt auf die Website des Casinos weiterleiten zu lassen. Um den Einzahlungsbonus beanspruchen zu können, ist für jeden der 3 Boni eine Mindesteinzahlung von 20 € erforderlich.
Als neuer Spieler können Sie im Vegadream Casino direkt mit einem Willkommenspaket nach Ihrer Registrierung durchstarten. Hierbei können Sie sich einen Bonus auf die ersten drei Einzahlungen sichern. Freispiele sind ebenso ein Bestandteil wie weitere lukrative Bonusangebote für Bestandskunden. Der Vorteil bei Vegadream ist, dass Sie keinen Bonus Code benötigen, um einen der Boni aktivieren zu können. Vegadream Casino wird von Gammix Ltd. betrieben, einer vertrauenswürdigen Glücksspielgesellschaft, die mehrere Online Casinos betreibt. Der Anbieter wird von der Malta Gaming Authority lizenziert, die als eine der angesehensten Glücksspielbehörden gilt und einen erstklassigen Schutz für die Spieler bietet.
Bis Zu €500 Match Bonus (Exclusive VIP Silver Club) de Vegadream Casino
Obwohl der Fokus in der Spieleindustrie zweifellos auf der Entwicklung von Online-Video-Slots liegt, gibt es immer mehr Unternehmen, die verstärkt an Live-Casino-Spielen arbeiten. Ganz grob lässt sich unser Portfolio in die Kategorien Neue Spiele, Slots, Megaways, Games mit hoher Volatilität sowie Jackpotspiele und Live Casino einteilen. Da ich großer Fan von Online Automatenspielen bin, fallen meine Vegadream Erfahrungen in dieser Kategorie sehr positiv aus.
- Wie bereits erwähnt, handelt es sich beim Vegadream Online Casino um ein lizenziertes Casino mit Lizenz nach maltesischem Recht.
- Trotzdem findet ihr eine gute Auswahl an Roulette sowie Kartenspielen à la Blackjack oder Poker und noch einiges mehr.
- Der maximale Spieleinsatz pro Runde ist mit einem aktiven Bonus jedoch auf 4€ beschränkt.
- Um den Einzahlungsbonus beanspruchen zu können, ist für jeden der 3 Boni eine Mindesteinzahlung von 20 € erforderlich.
- Slots zählen sowohl im stationären Casino als auch im Online Casino zu den echten Klassikern.
Das Vegadream hat dies zum Glück erkannt und bietet euch eine solide mobile Option für unterwegs. Neben den kompetenten und freundlichen Dealern und der hohen Qualität der HD-Streams punktet die Online Spielothek in meinem Vegadream Testbericht erneut durch die Wahl der Spielanbieter. So bietet euch das Casino beispielsweise eine besonders große Auswahl an Spielen des Marktführers Evolution an.
Casino-Tischspiele
Die Translation wird aus einem speziellen Studio durchgeführt, alle Spiele sind von dem Leiter dieses Bereichs von Glücksspielen – Evolution Gaming präsentiert. Die Webseite vom Vegadream ist klassisch gestaltet – in schwarzer Farbe mit Gold. Auf der Startseite befindet sich ein großer Banner mit Werbung der verfügbaren Aktionen, darunter – ein Spielabschnitt der Spielplattform. Die Menütaste befindet sich in der rechten Oberecke, dort gibt es auch interaktive Links für die Navigation.
- Am besten verwenden Sie hierfür einfach unseren Link, um sich direkt auf die Website des Casinos weiterleiten zu lassen.
- Zu den beliebtesten Spielen zählen beispielsweise Wild Frames, Razor Shark, Jammin Jars, Deadwood, Dead or Alive 2, Tombstone, Tiki Tumble, Honey Rush sowie Gonzons Quest.
- Die Webseite widerspiegelt sich dann in einem für die kleinen Bildschirme optimierten Regime und sichert ihre Funktionalität.
- Die Online Spielautomaten unterscheiden sich nach der Funktionalität, Gameplay, Thematik und anderen Kennzeichen.
- Obwohl das Vegadream Casino erst 2021 an den Start ging, konnte der Anbieter in den letzten Jahren auf ganzer Linie überzeugen.
Die meisten Spiele können Sie ohne Echtgeld kostenlos auf unserer Casino Seite ausprobieren, noch bevor Sie Ihr Konto erstellen. Im Live-Casino treten Sie gegen echte Dealer an und können bei echter Casino-Atmosphäre Ihr Können unter Beweis stellen. Ihre Lieblingsspiele finden Sie schnell und unkompliziert über das Suchfenster. Wenn Sie sich bei der Suche lieber mehr Zeit lassen möchten, können Sie Ihr Wunschspiel auch nach Kategorie sortiert suchen und finden.
FAQs zu unseren Vegadream Casino Erfahrungen
Ebenso durchleuchten wir die Bonusbedingungen und zeigen Ihnen etwaige Fallstricke auf, die es beim Spielen mit einem aktiven Bonus zu beachten gilt. Eines der wichtigsten Tools für ein ausbalanciertes Zocken im Online Casino ist der Selbstausschluss. Das heißt, Sie können mit einem Tool auf unserer Plattform selbst festlegen, ob und für welchen Zeitraum Sie sich vom Spielen ausschließen. Dieser Zeitraum kann bei einem Tag, mehreren Tagen, Wochen oder Monaten liegen – Sie entscheiden selbst, wieviel Abwesenheit Sie vom Online Casino benötigen. Bitte beachten Sie, dass in dieser Zeit keine Einzahlung und keine Auszahlung möglich ist und Sie nicht auf Ihr Spielerkonto zugreifen können. Sobald die Bedenkzeit abgelaufen ist, aktivieren wir wieder Ihr Konto für Sie.
- Das einzige was Sie brauchen ist ein Internetzugang sowie einen gängigen Browser (z.B. Edge, Chrome, Firefox), mit dem Sie das Vegacasino aufrufen können.
- Ein gutes Casino kommt heute nicht mehr ohne vernünftige Mobile App aus.
- Auf unserer Seite kannst du deine Lieblingsgames auch nach deinen Wunsch-Herstellern filtern.
Ab 20 Euro Einzahlung auf Ihr Spielerkonto, kommen Sie in den Genuss von unserem attraktiven Einzahlungsbonus. Hier können Sie einen Cashback in Höhe von bis zu 1.650 EUR kassieren sowie 100 Cash-Spins für Ihre Games nutzen. Dazu gehört beispielsweise, dass der Einzahlungsbetrag bei 20 Euro oder mehr liegen muss und der Casino Bonus nicht übertragbar ist.
Geschichte des Vegadream Online-Casinos
Außerdem haben wir keine Beschwerden über kein ehrliches Spiel oder Probleme mit der Auszahlung der Geldmittel gefunden. Zum Nutzen der Gesetzlichkeit und Legalität der Arbeit vom Vegadream Casino spricht auch die Liste der Anbieter, die mit der Spielplattform zusammenarbeiten. Darunter sind die weltbekannten Entwickler, wie Yggdrasil, Wazdan, Thunderkick, Evolution Gaming. In unserem ausführlichen Casino Test zum Vegadream Casino haben unsere Experten sich von einer großartigen und abwechslungsreichen Spielauswahl überzeugen können.
- Sie können auch entscheiden, ob Sie sich die Gewinne auszahlen lassen möchten.
- Beachten Sie, dass Sie Ihr Bonusgeld 30 Mal umsetzen müssen, bevor Sie eine Auszahlung beantragen können.
- Alle Besucher von BestBettingCasinos.com erhalten einen exklusiven Bonus ohne Einzahlung bei Vegadream Casino.
- Nachfolgend zeigen wir Ihnen, wie sich der Willkommensbonus im Detail zusammensetzt.
- Die Wettanforderung für den zweiten Einzahlungsbonus beträgt nur das 25-fache des Bonusbetrags.
Es gibt keine Gewinngrenzen und Sie können mit diesem Bonus alle verfügbaren Spiele spielen. Beachten Sie, dass Sie den Einsatz innerhalb von 30 Tagen nach Erhalt des Bonus abschließen müssen. Vegadream gibt Ihnen 200% zusätzliches Spielgeld auf den Betrag Ihrer Einzahlung. Wenn Sie jedoch 200 € einzahlen, können Sie mit 600 € spielen. Verwenden Sie diese Gewinne, um den maximalen Bonus für die 2.
Bis Zu €250 Match Bonus (Exclusive VIP Gold Club) de Vegadream Casino
Es ist toll, dass die Spielauswahl auf dem Handy fabelhaft ist und Sie Tausende von Slots unterwegs genießen können. Sie müssen dafür keine Mobile App herunterladen, sondern können direkt über den Browser auf das Casino zugreifen. Ein lästiger und zeitaufwendiger Download einer App entfällt somit. Ebenso sind alle Funktionen des Spielerkontos sowie die Ein- und Auszahlungen verfügbar. Damit Sie eines der umfangreichen Bonusangebote, die wir Ihnen in unseren Vegadream Erfahrungen vorgestellt haben, nutzen können, ist vorab natürlich eine Anmeldung erforderlich. Wie Sie den Bonus aktivieren und nutzen können, verraten wir Ihnen nun.
- Diese Verschlüsselung erlaubt es Ihnen, Ihre Daten ohne Zugriff von Dritten an Vegadream zu übertragen.
- Die mobile Version ist für die Nutzer iOS, Android, Microsoft, Mac OS dank der Benutzung der Technologie HTML5 verfügbar.
- Sollten Sie einmal technische Fragen haben, können Sie uns gerne per Mail oder über unser Kontaktformular erreichen.
- Trotzdem ist es möglich, das Bonusgeld zu nutzen, um im Live-Casino zu spielen.
- Bitte beachten Sie, dass in dieser Zeit keine Einzahlung und keine Auszahlung möglich ist und Sie nicht auf Ihr Spielerkonto zugreifen können.
Und das ist noch nicht alles, denn Sie erhalten zusätzlich zu dieser 2. Bei Vegadream können Sie Ihre erste Echtgeldeinzahlung verdoppeln. Sie müssen nur eine Einzahlung zwischen 20 € und 550 € tätigen. Wenn Sie sich für eine Einzahlung von echtem Geld entscheiden, können Sie aus einer Reihe von sicheren und zuverlässigen Zahlungsmethoden wählen.
Woran erkennt man, dass das Vegadream Casino seriös ist?
Das Casino nimmt das Thema verantwortungsvolles Spielen sehr ernst und bietet den Spielern eine Reihe von Optionen, um sicherzustellen, dass sie immer verantwortungsvoll spielen. Diese Website bietet Ihnen als Spieler ein unglaublich benutzerfreundliches Design für eine einfache Navigation. Auf der Homepage von Vegadream sind Spielkategorien direkt zu sehen. Ein Dropdown-Menü auf der rechten Seite ermöglicht den Zugang zu den Abschnitten “Zahlungen” und “Werbeaktionen”. Am Ende der Homepage finden Sie die allgemeinen Geschäftsbedingungen sowie weitere Informationen über den Eigentümer und die Lizenz des Casinos.
- Das Vegadream Live Casino bietet eine Vielzahl an unterhaltsamen Spielen wie Blackjack, Roulette, Baccarat, Poker, Craps, Sic Bo und mehr.
- Unser Fazit ist, dass dieses Online-Casino alle Anforderungen erfüllt, die man an ein modernes Casino stellen kann.
- Das heißt, von der ersten Codezeile bis zum Release wurde die Darstellung der Games auf mobilen Endgeräten wie Smartphones und Tablets in den Vordergrund gerückt.
- Und das ist noch nicht alles, denn Vegadream gibt Ihnen auch einen großzügigen Bonus auf die ersten 3 Einzahlungen, die Sie tätigen.
Es gibt über 90 Online Spielautomaten in dieser Casino-Kategorie mit einer Bonuskauffunktion. Man braucht nicht zu warten, bis die Bonusrunde sich mit einer erfolgreichen Kombination der Symbole öffnet, man braucht nur zu bezahlen und der öffnet sich sofort. Casino ist auf Deutsch, Englisch, Norwegisch und Finnisch verfügbar. Die Information über die Lizenz, Arbeitsbedingungen und andere nützliche Informationen befinden sich im Unterteil der Seite.
Bonusbedingungen für den Bonus ohne Einzahlung
Dadurch wird sichergestellt, dass Spieler auch auf kleineren Bildschirmen ein unvergessliches Spielerlebnis erleben. Mehrere Spielestudios haben ihre Jackpot-Spiele für die Nutzung bei Vegadream integriert, darunter fast ein Dutzend progressive Mega-Jackpot-Slots von Microgaming, wie z. Auch ihre Wowpot-Spiele, wie Sisters of Oz und The Queen of Alexandria, sind erhältlich.
- Ebenso wie sich der Bonus auf die ersten drei Einzahlungen staffelt, so staffeln sich auch die Umsatzbedingungen.
- Leider gibt es bei der Kategorisierung noch Nachbesserungsbedarf.
- Die Auszeichnungen werden als Geld aufs Bonuskonto und Free Spins im Vegadream Casino eingezahlt.
- Wir bieten eine große Auswahl an Spielen, einige Klassiker wie Book of Shadows, aber auch echte Raritäten, von denen selbst High Roller noch nie gehört haben.
- Eine spezielle Casino-App ist auch nicht nötig, um über das Handy oder Tablet auf das Spielangebot des Casinos zugreifen zu können.
Neben Live-Casinospielen können Sie auch Live-Spielshows spielen. Auf Ihrem Bildschirm können Sie tolle Spiele mit einem menschlichen Casino-Moderator spielen. Wir lieben es, live Monopoly, Gonzos Schatzsuche und Dream Catcher zu spielen. Diese Spiele sind fantastisch und mit ein bisschen Glück gewinnen Sie eine Menge Geld. Sie können die 100 Freispiele für Book of Dead oder Book of Shadow verwenden. Wählen Sie einen der Spielautomaten und finden Sie heraus, wie viel Geld Sie gewinnen werden.
Slots
Als Vegadream Casino sind wir fest entschlossen dem entgegenzuwirken und unseren Kunden eine sichere Umgebung zu ermöglichen, in der Sie jederzeit Ihr Spielverhalten kontrollieren können. Ein Online Casino ist schließlich nur so gut wie seine Website und die dazugehörige Software. Meine Vegadream Erfahrung hierzu fällt ganz gut aus, es gibt aber noch Luft nach oben. Wobei ihr beachten solltet, dass es üblich ist, dass Rubellose einen relativ geringen RTP-Wert haben.
Populäre Spiele in dieser Kategorie sind Deadwood, Wild Frames, Razor Shark, Dragon Horn, Midas Golden Touch sowie Book of Shadows. Für viele Zocker und vor allem High Roller sind Live Spiele das Argument schlechthin, wenn es darum geht, in einem Online Casino ihr Glück zu probieren. Kein Wunder, denn so viel Casino-Atmosphäre lässt sich sonst nur im stationären Casino schnuppern.
Vegadream Live Casino
Leider gibt es bei der Kategorisierung noch Nachbesserungsbedarf. Beispielsweise wäre es schön, wenn die Tischspiele eine eigene Kategorie bekämen. So müsst ihr über die Suchfunktion gehen und habt keinen richtigen Überblick über das Angebot. Die Suche ist ebenfalls etwas gewöhnugsbedürftigt, funktioniert aber dennoch gut.
- Man braucht ein nötiges Zahlungssystem zu wählen und den Anweisungen im persönlichen Account zu folgen.
- Damit können Sie nicht nur am Desktop PC, sondern auch auf dem heimischen Sofa und von unterwegs Ihre Lieblingsspiele spielen.
- Für die Transaktionen sind viele Methoden verfügbar, es gibt keine Gebühren von der Seite der Plattform.
- Hierzu ist eine Einzahlung über mindestens 20 Euro erforderlich.
- Wenn Sie viel Geld gewinnen, können Sie auch viel Geld abheben.
Die gültige Glücksspiellizenz der Gammix Limited sorgt zudem für Vertrauen. Obwohl das Vegadream Casino erst 2021 an den Start ging, konnte der Anbieter in den letzten Jahren auf ganzer Linie überzeugen. Die Seite wird von der auf Malta beheimateten Gammix Limited betrieben, die schon seit längerer Zeit Erfahrungen im Glücksspielsektor hat. Sie haben alle wichtigen Genehmigungen, die ein Online-Casino im modernen Zeitalter haben sollte. Vielleicht eines der besten Updates der Website, bis jetzt, war die Veröffentlichung der mobilen Version, mit der wir das Vegadream nun auch auf mobilen Geräten erleben können.
